
The Finals of Guardians 2019 Is Over
This year’s Guardians 2019 gave more space to young people from Slovakia with diverse experience in the field of information security. The competition brings together people who have wide experience in this field with those who just would like to direct their carrier to the field of cybersecurity. More sophisticated attacks, more teams, real environment and a high-level team of professionals! Everything that was brought by the third year of the game Guardians 2019. Binary Confidence in cooperation with the National Unit SK-CERT of the National Security Authority prepared the competition in which young and smart people interested in information security could try, in the real environment, their skills to protect the election team against hacker attacks.
The qualification round in the form of a CTF (Capture The Flag) was in process from November 2018 till the beginning of February 2019. A total of 127 contestants were registered, of which 45 resolved at least a part of tasks. 13 tasks were set from the beginner to intermediate difficulty level. Contestants could try the tasks ranging from reverse engineering, steganography, and forensic analysis to application exploiting. The ten best players advanced to the final round and for the first time all of them met in the exercise on the premises of the National Security Authority at the beginning of March.
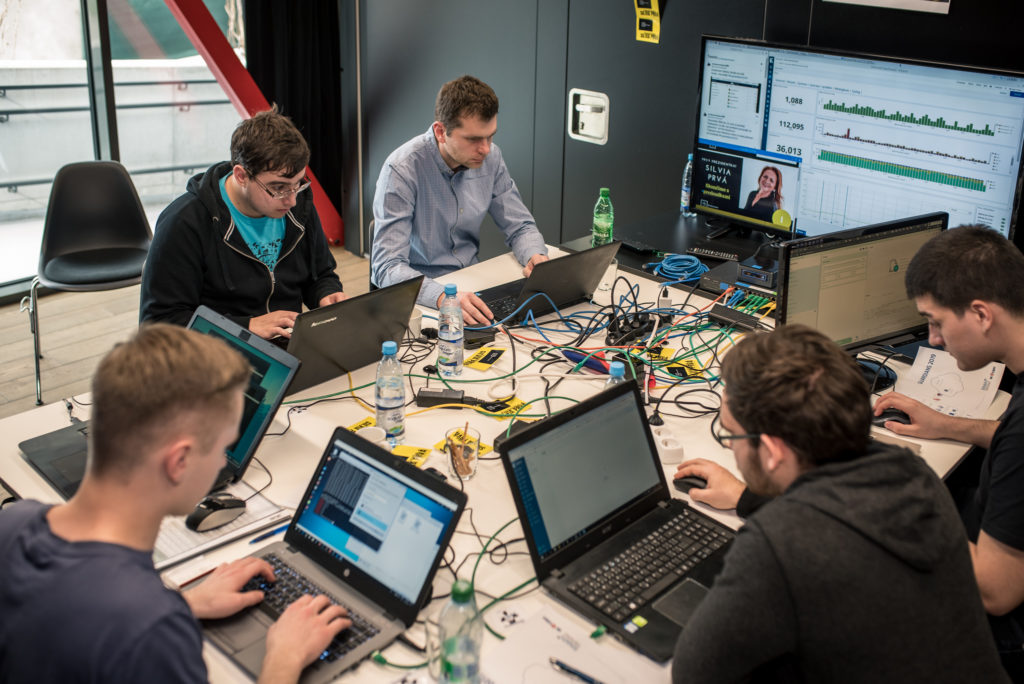
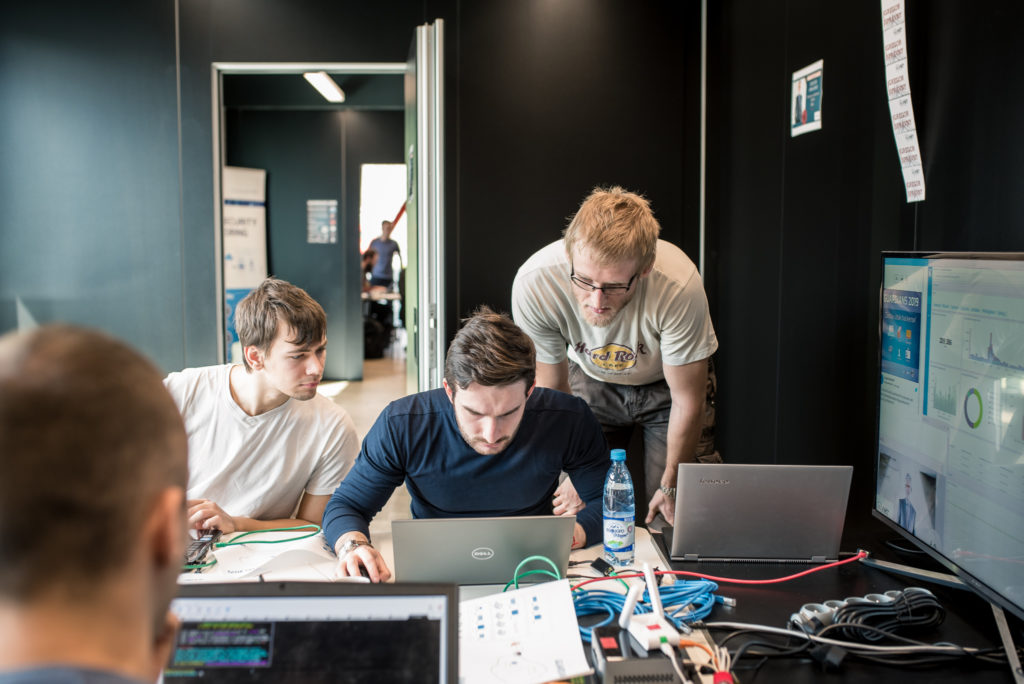
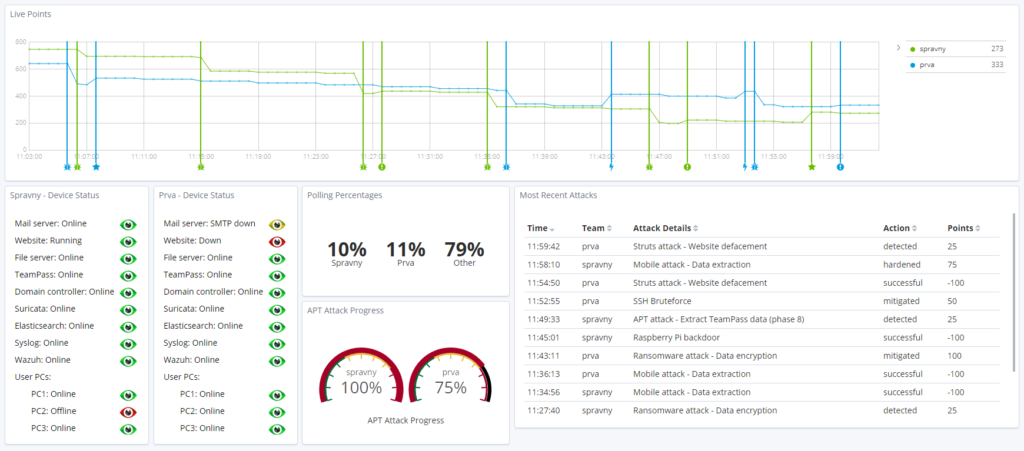
The final game took place on 15 March 2019 in Binary in Bratislava. Contestants divided to two teams withstood for five hours different attack forms on physical and virtual infrastructure of their candidate, protected it against attacker’s penetrations, against their attempts to change published information (webpage of the candidate), and against denial of services (e-mails, etc.). Attackers used different techniques, being used in real life and real infrastructures as well. In addition to the protection of the candidate’s infrastructure, the team coordination training was a very important part of the exercise. The only protector is obviously insufficient in more complex infrastructure and in dealing with concentrated effort of attackers. Only well-organized and well-working team of protectors with defined roles and set priorities can manage such situation.
Course of the game
Two promising presidential candidates – Gregor Right and Silvia First tried to defend themselves together with their election teams against hackers group – Octopus. They countered the attacks that may have influenced their run and the results of the election.
Our fictitious candidates in order to be protected against hackers, and having learned from several negative experiences when the election teams underestimated the protection against attacks, for example Google account abuse of John Podesta (a boss of Hillary Clinton’s election campaign) or the data leakage of German politicians in January 2019, hired IT security specialists who had to pass demanding qualification and training.
The game evaluation
Both teams were compatible in the course of the final game and quite successfully were dealing with the tasks and difficulties according to the exercise scenario. After all, with a slight margin, the team of Gregor Right candidate was more successful. The primary goal of Guardians 2019 is not to compete with the teams but to support the young talents who might be of benefit to cybersecurity field in the future. The issue of filling up the personnel capacities by experts for this field is still topical not only in Slovakia but also all around the world. For this reason there is a need to develop interest in cybersecurity topic among younger generation. The Guardians 2019 competition helps to motivate young people to improve their skills and to work up to the top in this domain which is constantly evolving and challenging the world.
Description of several attacks:
APT attack (Advanced Persistent Threat)
A malicious code penetrated into computers of the election team via the e-mail. It did nothing just waited for the instructions from Command and Control (C&C) server. After the instruction was submitted, it downloaded payload which performed different saboteur activities in the network: it stole passwords or opened the “tunnel” from the internet to the network of the election team and thus enabled the attackers to move around there and steal further.
Via mobile phone
A link to a malicious application was infiltrated via SMS message. This application was able to read or send SMS messages, to take photographs, to record videos from the room or to create voice recordings undetected.
Web application attack
The objective of this attack was to compromise the campaign and thus the candidate. Attackers tried to spoof the webpage content which unnoticeably spread forged messages.
Ransomware
Currently, one of the most widespread attacks that encrypts the data of the victim and asks a considerable financial reward for its decryption. Even that attack was experienced by defenders of the Guardians 2019 teams.
« Späť na zoznam





